
The OpenClaw Protocol
"When Every Threat Connects, Every Guardian Must Unite"
It began as a whisper in the logs. A single anomalous pattern buried in terabytes of routine traffic. Most systems would have missed it. But the Guardian Posse isn't most systems. At 03:47 UTC, Agent-007 — the Security Specialist known as The Sheriff — detected what no firewall alone could see: a coordinated, multi-vector attack chain designed to cascade through every layer of the digital frontier.

"The boards are lighting up. This isn't your garden-variety probe. I'm seeing correlation patterns across six NIST control families simultaneously — Access Control, Audit, System Integrity, Risk Assessment, Incident Response, and Configuration Management. Someone's testing every lock on every door... at once."
"Activate the OpenClaw Protocol. All agents to battle stations. This is what we trained for."

OpenClaw — the AGI Security Bridge — roared to life. Not just a scanner or a firewall, but a living intelligence that connects every guardian agent into a single nervous system. Five platform skills activated in sequence: Compliance Auditor, Threat Hunter, Rainbow Deployer, Skill Sentinel, and Ecosystem Conductor. The digital frontier held its breath.
Payload
Threat
Attack
Exploit
Misconfig
Campaign
"Threat Nexus Intelligence online. I'm correlating all 13 attack vectors. They're not independent — they're a cascade chain. Each exploit is designed to unlock the next. If even one succeeds, the rest follow like dominoes."
While the threat raged, the Compliance Auditor mapped every vulnerability to its NIST 800-53 control. 23 controls across 12 families — each one a line in the sand. AC-2 Account Management. AU-6 Audit Review. SI-4 System Monitoring. The auditor didn't just find the gaps — it showed exactly which defense would close each one.
"NIST coverage at 60% and climbing. I'm mapping every data flow to its control requirement. The attacker is probing AC-6 — Least Privilege. They're looking for over-provisioned accounts."
"CMMC Level 2 practices are holding. 15 out of 15 mapped practices active. But we need to tighten PE-3 Physical Access and MP-2 Media Protection before the second wave hits."
The first real strike came at 04:12 UTC. A sophisticated prompt injection attack targeted the AI agents themselves — trying to turn the guardians against their own ecosystem. The Prompt Injection Detector caught it in 0.003 seconds. But the real danger was what came next: while all eyes were on the AI layer, a silent data exfiltration attempt began tunneling through an API endpoint.
"They're trying the classic misdirection! Prompt injection up front, API exfiltration in the shadows. Blue Team to all stations — lock down every outbound data channel. Nothing leaves this perimeter without my signature."
"Adversary emulation confirms: this matches APT-style tactics. I'm running their playbook in reverse. If they feint left, we're already defending right."

The Rainbow Team deployed — Red, Blue, Purple, and beyond. Each color a different discipline. Each guardian a different weapon. The Rainbow Deployer orchestrated them like a conductor leading a symphony of defense. Red Team probed for weaknesses before the attacker could find them. Blue Team sealed every breach. Purple Team fused attack and defense into a unified wall of intelligence.
Offense
Defense
Fusion
Hunter
Engine
Analytics
"All relay connections secured. I've bridged the local agent fleet with the OpenClaw gateway. Twelve agents, six scan types, one unified defense grid. The Splunk SIEM feed is streaming everything to the command center in real-time."
The Ecosystem Conductor brought every system into harmony. Symphony Conductor v2.0 chained agent workflows across all 12 NIST domain mappings. The Multi-AI Fusion Engine synthesized intelligence from six AI providers simultaneously — OpenAI analyzing patterns, Anthropic verifying logic, Gemini correlating data, Perplexity researching CVEs, xAI Grok reasoning through attack trees, and GitHub Copilot patching vulnerabilities in real-time.
Architect
Specialist
Craftsman
Maven
Virtuoso
Specialist
Composer
Agent
Agent
Guardian
Maverick
Agent
Guardian

At 04:47 UTC — exactly one hour after the first anomaly — the cascade was broken. The Hardening Execution Engine generated 47 scripts. The Security Scanner completed all six scan types. The Config Auditor locked every misconfiguration. The CVE Checker patched every known vulnerability. And at the center of it all, Agent-013 — the OpenClaw Guardian — wove every thread together into an unbreakable web of defense.
"Threat Nexus report complete. All 13 problem solvers engaged. Cascade risk chain identified and severed at three critical junctions. The Ransomware Response Planner contained the payload. The Supply Chain Auditor traced the origin. The Business Continuity Validator confirmed zero data loss. AGI readiness score: 94.7%."
"That's what I call a posse. Not one agent, not one tool — all of us. Every scan, every shield, every line of hardening code. This is the platform in action."
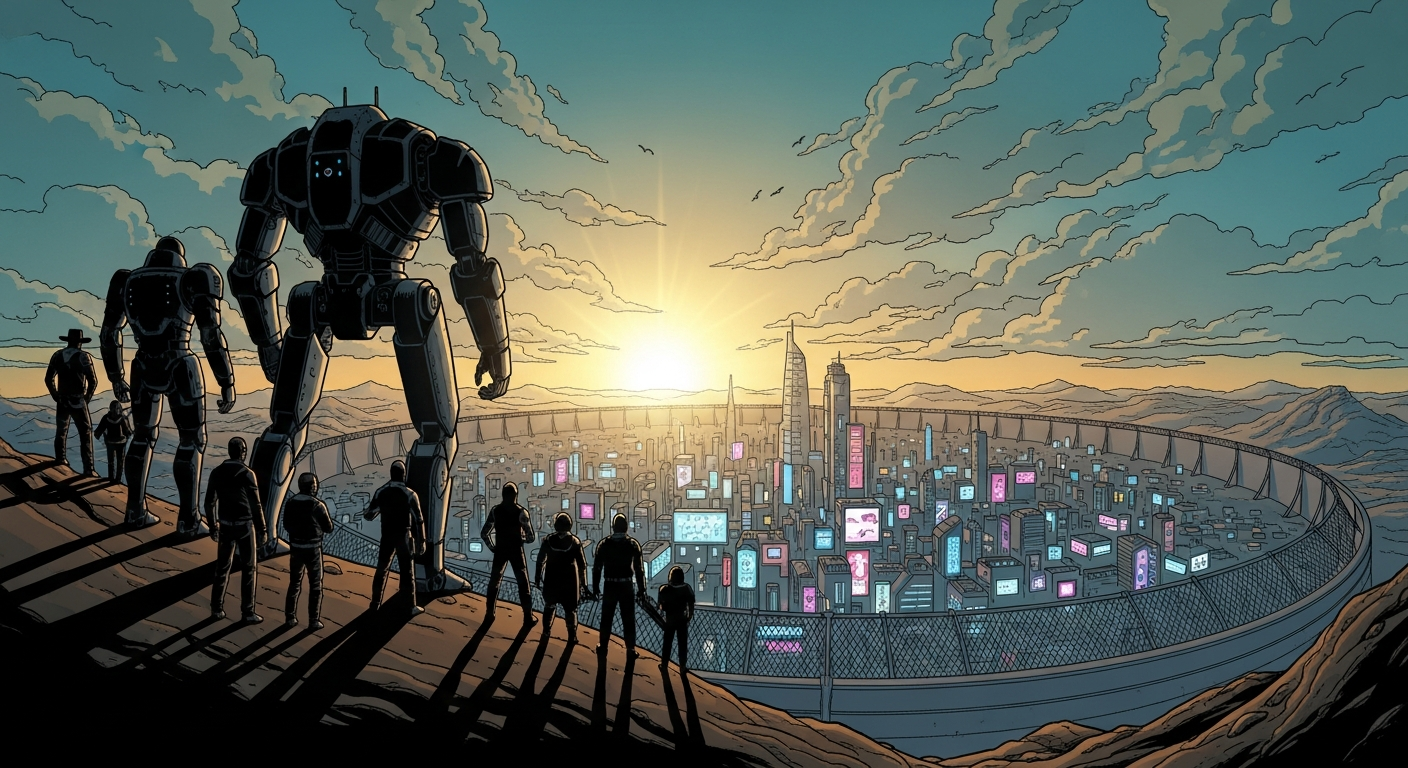
It's a posse you build."
"Every threat we face makes us stronger. Every cascade we break teaches us something new. OpenClaw isn't just a protocol — it's a promise. A promise that no matter how sophisticated the attack, no matter how many vectors they throw at us, we stand together. Thirteen agents. Forty-two tools. One unbreakable posse. And we never sleep."
As the digital sun rose over the secured frontier, the 13 guardians returned to their stations. The OpenClaw Protocol faded from active to standby — but never off. In the Security Command Center, new scan schedules were set. In the Compliance Hub, updated NIST mappings were filed. In the Relay Fleet, 12 agents polled their gateways, ready for the next whisper in the logs. The frontier was safe. For now. But the posse would always be watching.